---
title: "From Zero to Hero: Identity Edition"
description: "There are tons of identity resources out there. What if you had a curated list of resources? Then, keep reading this blog post!"
authors:
- name: "Carla Urrea Stabile"
url: "https://auth0.com/blog/authors/carla-stabile/"
date: "Dec 13, 2023"
category: "Developers,Tutorial,Identity"
tags: ["identity", "authentication", "authorization", "auth0"]
url: "https://auth0.com/blog/from-zero-to-hero-identity-edition/"
---
# From Zero to Hero: Identity Edition
Identity is a broad topic, and many resources are available. This blog post gives you a curated list of some of the most relevant resources at Auth0 by Okta and relevant identity organizations.
## Identity Fundamentals
A [digital identity](https://auth0.com/docs/glossary#digital-identity) is a set of attributes that define a particular user in the context of a function that is delivered by a specific application.
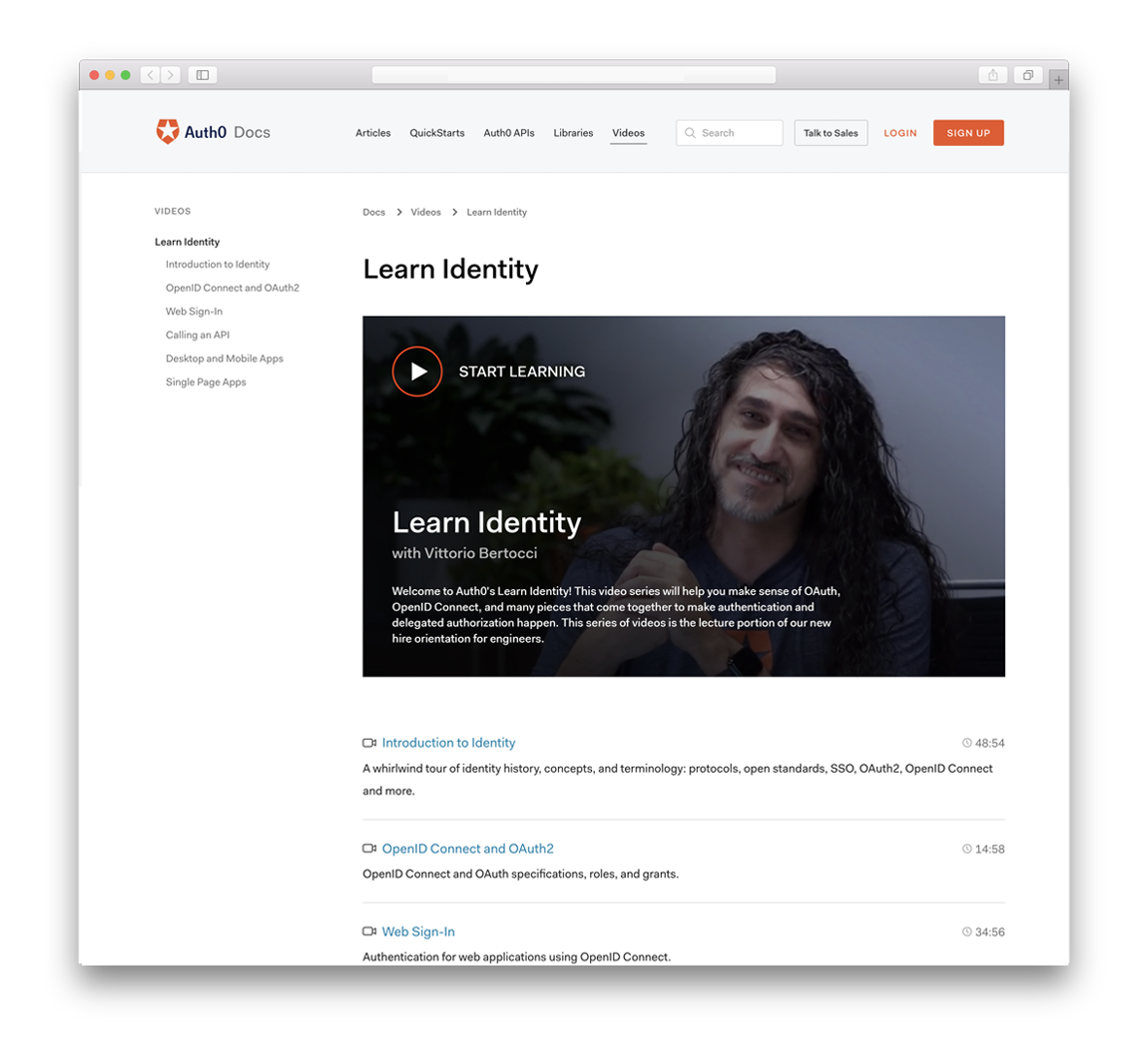
### Learn it from Vittorio
[Identity Fundamentals Course](https://auth0.com/docs/videos/learn-identity-series) brought to you by the one and only [Vittorio Bertocci](https://auth0.com/blog/in-celebration-of-vittorio-bertocci/).
### IAM, CIAM, Am I?
- [Identity and Access Management](https://auth0.com/docs/get-started/identity-fundamentals/identity-and-access-management) provides control over user validation and resource access, and it's commonly known as IAM.
- [Customer Identity and Access Management (CIAM)](https://auth0.com/blog/what-is-ciam/) how companies give their end users access to their digital properties as well as how they govern, collect, analyze, and securely store data for those users.
### No Time? Learn Identity In a Minute
- [Identity In a Minute Series](https://www.youtube.com/playlist?list=PLshTZo9V1-aHPyYQeq7skl2Y8lcANtvcI) is an ongoing series of 60-second shorts that describe key concepts in modern identity management, authentication, and authorization.
### More Time? Learn Directly from Identity Experts
- [Identity Unlocked Podcast](https://identityunlocked.auth0.com/): "Identity, Unlocked" is the podcast that discusses identity specs and trends from a developer perspective.
- [Authorization in Software Podcast](https://authorizationinsoftware.auth0.com/): "Authorization in Software" features chats with industry subject matter experts in authorization.
## Authentication
In [authentication](https://auth0.com/intro-to-iam/what-is-authentication), a user or application proves that they are who they say they are by providing valid credentials.
There are many ways of authentication, though. 🤔 Learn about the most common ones:
- [Username and Password Authentication](https://auth0.com/blog/username-password-authentication/)
- [Passwordless Authentication](https://auth0.com/blog/what-is-passwordless-authentication/)
- [SMS Passwordless Authentication](https://auth0.com/blog/sms-passwordless-authentication/)
- [What is Single Sign-On Authentication and How Does It Work?](https://www.youtube.com/watch?v=Vp6kx4Sd_E0)
## Authorization
[Authorization](https://auth0.com/intro-to-iam/what-is-authorization) is the process of giving someone the ability to access a resource.
People usually mix up [Authentication and Authorization](https://auth0.com/intro-to-iam/authentication-vs-authorization) because authentication usually leads to authorization, but authorization does not always lead to authentication.
Learn more about authorization and the different types: 👇
- [What Is The Right Authorization Model For My Application?](https://auth0.com/blog/whats-the-right-authorization-model-for-my-application/)
- [What is Role-Based Access Control (RBAC)?](https://auth0.com/intro-to-iam/what-is-role-based-access-control-rbac)
- [What is Fine-Grained Authorization?](https://docs.fga.dev/intro/authorization-and-okta-fga#what-is-fine-grained-authorization-fga)
- [Permissions, Privileges and Scopes - What's the Difference?!](https://youtu.be/vULfBEn8N7E?feature=shared)
## 2FA, MFA all-the-FA
There are many options you can use to prove your digital identity. These are called [**authentication factors**](https://auth0.com/blog/not-all-mfa-is-created-equal/#Factors--Authenticators--and-Assurance), and there are three main types:
- knowledge or something that you know, like a password,
- possession or something that you have, like a device
- inherence, which is something that you are or is inherent to you.
Usually, your application requires only one authentication factor to authenticate a user, typically a password. In some contexts, you may want more assurance about the user's identity. In that case, you can require two or more authentication factors. That's what two-factor authentication (2FA) and multi-factor authentication (MFA) are all about.
Learn more about 2FA and MFA 👇:
- [Two-Factor Authentication (2FA)](https://auth0.com/learn/two-factor-authentication)
- [The Working Principles of 2FA (2-Factor Authentication) Hardware](https://auth0.com/blog/the-working-principles-of-2fa-2-factor-authentication-hardware/)
- [The Working Principles of 2FA (2-Factor Authentication) Software](https://auth0.com/blog/the-working-principles-of-2fa-2-factor-authentication-software/)
- [2FA Using Biometrics](https://auth0.com/blog/two-factor-authentication-using-biometrics/)
- [Getting Started with Multi-Factor Authentication](https://auth0.com/learn/get-started-with-mfa)
## OAuth2, OIDC, Oh-what?
There are many standards used for identity. Some of the most relevant are OAuth2 and OIDC. OAuth 2.0, which stands for "Open Authorization", is a standard designed to allow a website or application to access resources hosted by other web apps on behalf of a user. At the same time, Open ID Connect (OIDC) is an authentication protocol that utilizes the authorization and authentication mechanisms of OAuth 2.0.
But what else is out there? Learn more here 👇
- [OAuth 2.0 Simplified](https://www.oauth.com/)
- [OAuth 2.0 and OpenID Connect (in plain English)](https://youtu.be/996OiexHze0?feature=shared)
- [OAuth in Five Minutes](https://youtu.be/KT8ybowdyr0?feature=shared)
- [An Illustrated Guide to OAuth and OpenID Connect](https://www.youtube.com/watch?v=t18YB3xDfXI)
- [OIDC Playground](https://openidconnect.net)
- [SAML Authentication](https://youtu.be/VzRnb9u8T1A?feature=shared): you can also use [samltool.io's](https://samltool.io/) playground to learn more
## Tokens, tokens, and more tokens!
A token is a piece of data that has no meaning or use on its own but, combined with the correct tokenization system, becomes a vital player in securing your application. There are different tokens, but what does each one do? How do you use them?
- [ID Tokens VS Access Tokens: What's the Difference?](https://youtu.be/vVM1Tpu9QB4?feature=shared)
- [What are Refresh Tokens?! and...How to Use Them Securely](https://youtu.be/LowJMwa7LCU?feature=shared)
- [Token-based Authentication Made Easy](https://auth0.com/learn/token-based-authentication-made-easy)
- [JSON Web Tokens](https://auth0.com/learn/json-web-tokens)
- [JWT.io](https://jwt.io)
## WebAuthn
WebAuthn is a W3C recommendation for defining an API enabling the creation and use of strong, attested, scoped, public key-based credentials by web applications to authenticate users strongly. Here are some great resources to learn more:
- [A Developer's Guide to WebAuthN](https://youtu.be/rsJcXHUZhRY?feature=shared)
- [Enable Passwordless Login using Biometrics](https://youtu.be/d18xx_OJJ7U?feature=shared)
## Passkeys
Passkeys are password replacements that provide a faster, easier, and more secure user login experience that leverages WebAuthn under the hood. Learn more about passkeys:
- [webauthn.me/passkeys](https://webauthn.me/passkeys)
- [Our Take on Passkeys](https://auth0.com/blog/our-take-on-passkeys/)
- [Passkeys in Action](https://www.youtube.com/watch?v=SWocv4BhCNg)
- [passkeys.dev](https://passkeys.dev/)